 Reading Time: 9 minutes
Reading Time: 9 minutes
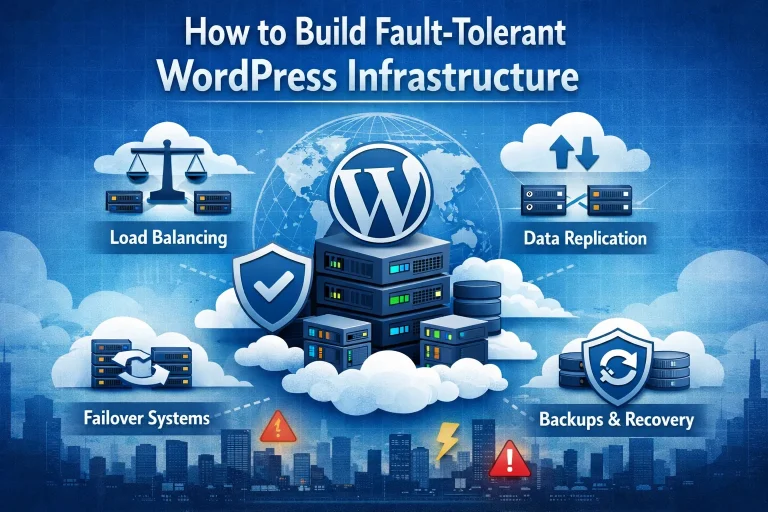
The appeal of creating a small business website with WordPress is always going to be centered on the simplicity and cost-effectiveness of using the platform. You’ll be paying immeasurably less than what you’d probably need to give to a web designer to have them build your website, and it’s really quite simple to build it yourself with WordPress. But it’s one thing to put a site together and another to have it build to the extent that you can always rely on it to be fully functioning and best serving your online business interests. A lot of having that consistent performance will be tied into high availability WordPress hosting, and it’s also good to know how to build fault-intolerant WordPress infrastructure. So that’s what we will look at with this week’s blog entry here. At any given time there’s a whole host of people who are putting together a WordPress website for the first time, and it may well be that some of them are having their website hosted by us here at 4GoodHosting. If that’s the case then we need to stress the superiority of Managed WordPress hosting for fault tolerance, as there are all sorts of areas where you’re safeguarded if you have website optimization taken care of for you. Part of receiving this service is having your host conduct regular site overviews and checking for any instances of sub-par performance or component failures. Starting at the the start it may be necessary to define what are WordPress faults and what it means to have fault tolerance for your website. These faults are everything from connection errors to slow speeds, 404 errors, and the colloquially well-known ‘white screen of death’ that can occur if a WordPress site has any type of code that becomes misconfigured after it was initially created. High availability WordPress hosting means there is less of a chance of that happening, but if you’re going to take on these issues yourself you’ll need to be proficient with debugging tools, component deactivation, and / or knowing how to increase memory limits. Tall order for some, so what’s best is to build your infrastructure to be fault-tolerant...