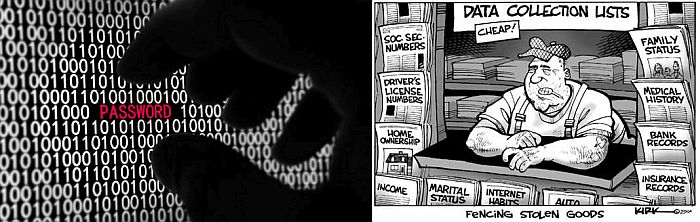
Is your website becoming much more popular? If you are searching for reliable yet inexpensive, and fast loading website hosting, “shared web hosting” or “V.P.S.” (Virtual Private Server hosting) service are two good, but not identical, options. The most common choice, to do it at rock bottom costs, shared hosting, but for many businesses the limitations of shared hosting eventually becomes outgrown. Migrating from a shared server plan to a VPS (or an entirely “Dedicated” or “Standalone Server) is typically the next step. 4GoodHosintg provides free upgrade migration services; to solve any nervousness when you may decide to upgrade your website to its own server. Some signs you have outgrown Shared Web Hosting: Skyrocketting Traffic For low traffic websites shared hosting is ideal. If you are noticing your traffic increase consistently, or if you are offering high-bandwidth content such as video(s); you may need to upgrade to a VPS (Virtual Private Server) for dedicated bandwidth, and for a lower-latency (faster) less congested network connections. When your business/website grows in size: your email, disk space, CPU & RAM (Random access memory) requirements will also eventually surpass your existing shared hosting plan. The growth of your business will often dictate the need for upgrades. Choosing between VPS and dedicated server Perhaps you would feel best serving your website by renting your own private server (standalone web server with it’s own dual power supply). However, first consider the differences between VPS and Dedicated servers - to find out which one is best for your application; including cost, as VPS are less expensive than leasing dedicated equipment in our data center. In either case, 4GoodHosting offers numerous advantages: such as 24/7 customer support, “RAID” hard drive and SSD redundancy, dual-coast back-ups, disaster recovery servers, plus the flexibility of upgrading or downgrading your server hosting package whenever you need with free migrations. read_more Maximum Security of your data If your business or organization is dealing with alot of company confidential data - then you should ensure the security of your data. By choose self-contained VPS or Dedicated Server hosting, you will more secure control over who has the ability to access your data. For VPS...