OpenVPN has become the most widespread VPN (Virtual Private Network) protocol used by today’s commercial VPN providers.
However, did you know you can set up your own VPN service on a VPS (Virtual Private Server) which provides a closed environment situated as a physically remote server?
If you lease a VPS from 4GoodHosting you can do anything you want with it, such as installing any operating system, and basically treating the VPS as your own personal remote server.
If you are interested in running a VPN service on your VPS then this article will be helpful.
Using automated installation scripts, the process has become easier for the average person to use. The following is how to install OpenVPN on your own VPS server running Centos 6.x or 7, Debian (or Ubuntu) Linux.
- download an auto-installer for OpenVPN, such as this one openvpn-install
- Next: login to your VPS (as root) and run the following:
- wget http://git.io/vpn --no-check-certificate -O openvpn-install.sh; chmod +x -openvpn-install.sh;
If you are not logged in as root you type: sudo ./openvpn-install.sh
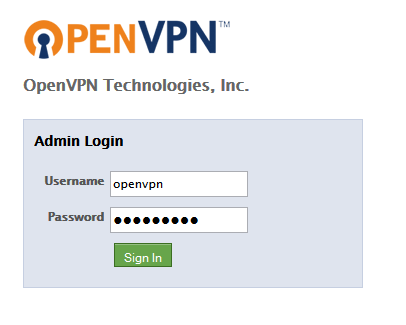
The OpenVPN auto installer will execute and it will then prompt you for more information as follows:
1. The script will first autodetect your public IP address. (if you have multiple IP addresses on your VPS you can set it via the script to utilize a specific one.)
2. Next, type in the port number used for incoming OpenVPN connections (or use the default of “1194”). Any port can be used, any random one will likely do - as long as it is not in-use by other application server, or service. Select whether to listen on port 53 too; which is useful for covert connections.
3. Next, you will be asked for a name of client certificate. You can use anything such as “user1”, “anonymous”, “johndoe”, yourdog’s name, etc.
That’s all the OpenVPN installer needs to know. Subsequently it will download the packages, generate the encryption keys and certificates and then after that it will attempt to start the server. OpenVPN uses 2048bit RSA keys for authentication and the 128 bit Blowfish algorithm for data encryption.
If everything went smoothly, the auto-installer will notify you that the security client certificates have been saved into a .tar.gz archive, e.g. “ovpn-client.tar.gz”.
read_more
How can you check if your OpenVPN server is running?
Type this command: > ps ax|grep openvpn
Something like this should appear:
6646 Ss 0:00 /usr/sbin/openvpn --writepid /var/run/openvpn.server.pid --daemon ovpn-server --cd /etc/openvpn --config /etc/openvpn/server.conf
Next traffic forwarding has to be enabled.
Edit /etc/sysctl.conf Enable ipv4 forwarding by un-commenting this line
“net.ipv4.ip_forward=0” by removing the # sign and changing 0 to 1 so it looks like this:
net.ipv4.ip_forward=1
Next save the file and activate the changes: sysctl -p /etc/sysctl.conf
Also enable masquerading in firewall iptables -t nat -A POSTROUTING -s 10.8.0.0/24 -o eth0 -j MASQUERADE
Now that the server is running you also need to install OpenVPN on your PC in order to take advantage of it.
You can download the OpenVPN client here (Windows installer):
http://openvpn.net/index.php/open-source/downloads.html
After you install it on your desktop or laptop: transfer the “ovpn-client-x.tar.gz” and unpack it to your OpenVPN GUI’s config folder ( typically in “C:\Program Files(x86)\OpenVPN\config\” )
Start OpenVPN client needs to be Run as Administrator (it won’t work if you don’t install it as administrator). Finally find the OpenVPN System Tray icon and then click connect.
That’s is about it, fairly easy for any novice system admin to install, yet the results are remarkable. You are now surfing the web with your VPS as the front-end interface to the world wide web. Your home PC is protected, and your internet activity will only be tracked using the VPN’s IP address.

Advantages of VPN on a VPS
- * The VPN provides a private IP address, so the IP address will not be blocked by services such as Youtube or Netflix or Hulu, or by most firewalls. This makes it an anti-censorship tool (although will not defend against other censorship measures such as packet sniffing).
- * VPN’s act as proxy servers (but also with encrypted connections from your PC to the VPN-VPS, therefore good for accessing georestricted services (as long the VPS is located in the appropriate country in which you wish to access the services from.)
All traffic between your computer and the VPS goes through an encrypted VPN tunnel. As long as the VPS is located outside an adversary’s area of influence (for example if someone in Iran wishes to evade government censorship and so sets up a VPS server located in Europe) it will provide a high degree of privacy. - * VPN on VPS also protects against hackers when using public WiFi hotspots
- * Can be cheaper than VPN.
Disadvantages
- * Because your VPS provides a static IP address which is associated to you, a global antagonist (such as the N.S.A. or police-state forces with an international reach) can easily trace internet such activity back to you. However, if you are not doing any wrong, then you shouldn't have to worry too much.